Why is it important for the traders to know what is spoofing on the exchange? Learn in this article:
- How spoofing works;
- Responsibility for spoofing;
- ATAS templates for detecting spoofing;
- Conclusions.
Spoofing is an intended manipulation with market prices with the help of posting and further fast withdrawal of big sell or buy orders. We will show you in a scheme how spoofing works using an oil market example.
How it works
As a rule, spoofing is done by robots.First, it automates necessary processes. Second, it excludes the human factor and works smoothly in accordance with the set algorithm. Let us consider a possible situation in the Brent oil market.
Let us imagine that we are oil market manipulators and we manage big money. Let us assume that the Brent price quote is 115.90 at the moment. We want to buy 17 lots at USD 115.86 and sell later 2-3 ticks higher. In order to reduce the price we create an impression of appearance of major sellers. To make this impression we post three significant limit sell orders:
- 122 lots at 115.89;
- 85 lots at 115.88;
- 54 lots at 115.87.
Remember that we want to buy 17 lots only and we posted 261 sell lots just in order to mislead other traders and trading robots and make them believe that a serious bearish interest has emerged in the market.
Appearance of our orders sharply increases the general number of all sell orders. Trading robots start to sell and the price quote goes down to USD 115.86. As soon as the price achieves the required level, the limit buy order for 17 lots is executed in two parts – 3+14
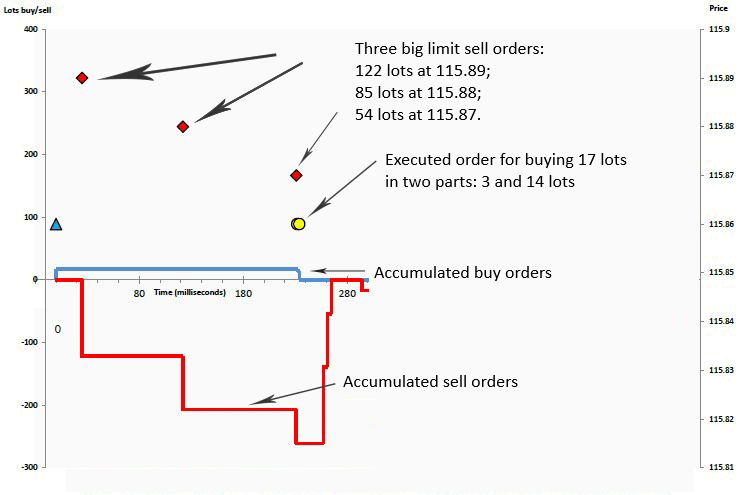
- Left axis is a number of lots. Long positions are positive numbers and short positions are negative numbers;
- Right axis is the price in USD;
- Horizontal axis is time in milliseconds;
- Red diamond symbols are big limit sell orders, which we do not plan to execute.
Our big orders for selling 122, 85 and 54 lots are automatically cancelled at the moment of execution of the order for buying 17 lots (blue triangle). By so doing, the general number of sell orders sharply decreases and it turns out that there is no major seller in the market any more!
Instead, we have 17 Brent oil lots, which we want to sell 2 ticks higher in order to make fast profit in this trade. Acting similarly, we will create an impression of appearance of a major buyer and post significant buy orders:
- 99 lots at 115.82;
- 88 lots at 115.83;
- 122 lots at 115.86.
Remember that we have just 17 lots, which we want to sell. We do not plan to execute the other limit orders for buying 309 lots. We know beforehand that we will cancel them – namely this trick is called spoofing.
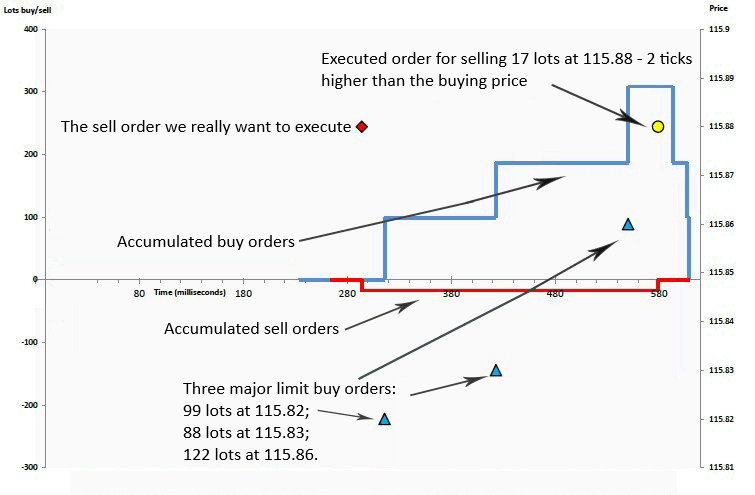
Our big orders for buying 309 lots are cancelled automatically at the moment of execution of the order for selling our 17 lots. By so doing, the general number of limit buy orders sharply decreases.
Profit in 2 ticks in the oil market for this volume is USD 340 in 350 milliseconds. Impressive? Definitely, especially if we take into account that you can spoof several times during a day.
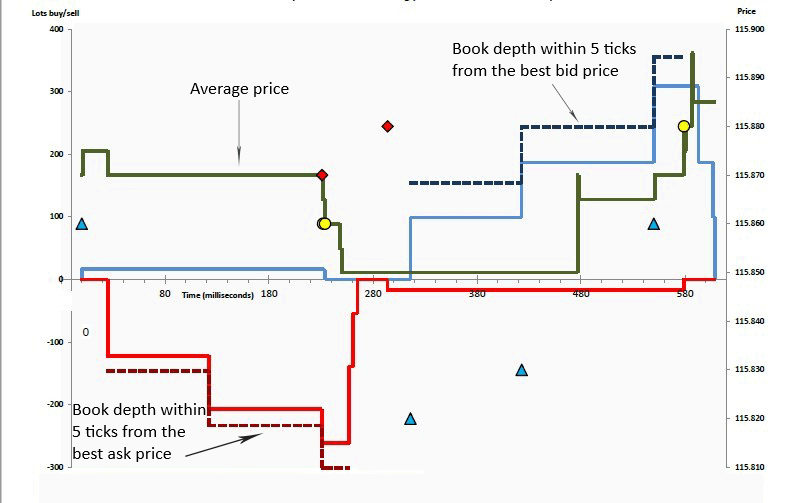
This is spoofing or market price manipulation because:
- the limit sell orders, posted by us, constituted 87% of all sell orders within 5 ticks from the best bid price (what bids and asks are). Emergence of our orders decreased the price;
- the limit buy orders, posted by us, constituted 88% of all buy orders within 5 ticks from the best ask price. That is why emergence of our orders increased the price.
Compare the book depth and cumulative number of orders and you will immediately realize why the price moved in the required direction.
It is impossible to execute such trades within such a short period of time manually. Due to this, we make a conclusion that high-frequency algorithms post orders.
Responsibility for spoofing.
One of the most famous spoofers is Igor Oystacher. There is a lot of information about him in the Internet, that is why we will not write about him.Here’s another example. Heet Khara and Nasim Salim were ordered by the Federal Court to pay a combined penalty in the amount of USD 2,69 million for spoofing in the gold and silver futures markets. It is interesting that they are UAE citizens. The US Commodity Futures Trading Commission (CFTC) wrote in the press-release related to this case that it will protect US futures markets and sue infringers wherever they are located. CFTC proved that Heet Khara and Nasim Salim posted major orders without real intentions to buy/sell, planning to cancel them beforehand, that is, having the only goal to manipulate the gold and silver market prices during the period from February to April 2015. Apart from a huge penalty, the court prohibited them from trading in the American markets forever.
It is rather difficult to prove spoofing, because it is required to reason that a trader, when posting a big order, had no intention to execute it, but only wanted to manipulate the price. CFTC studies electronic and paper correspondence in order to detect cheating intentions and conducts statistical analysis of trades.
They also fight spoofing in Russia. The Central Bank (CB) of RF develops models of fighting spoofing together with exchanges.
ATAS templates for detecting spoofing.
There is a template (the file with .dom extension) in the trading and analytical ATAS platform for detecting spoofing.Let us consider in detail how to set and use it.
- Launch Smart Dom from the main window of the platform;
- select an instrument – for example, 6E;
- load the spoofing template for Smart Dom.
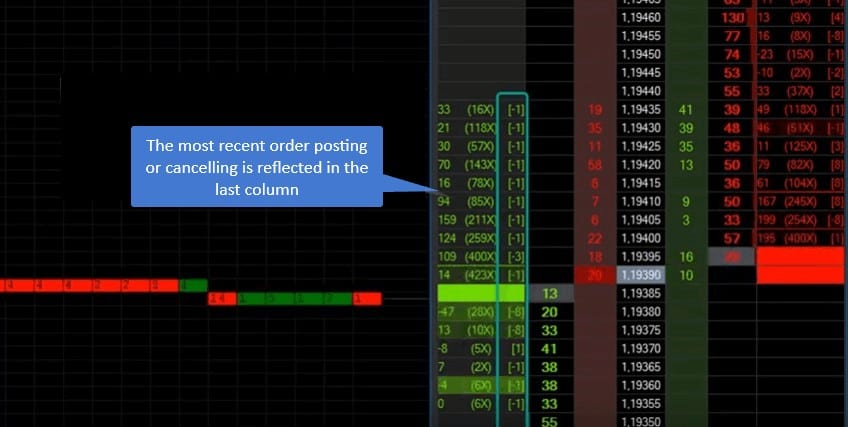
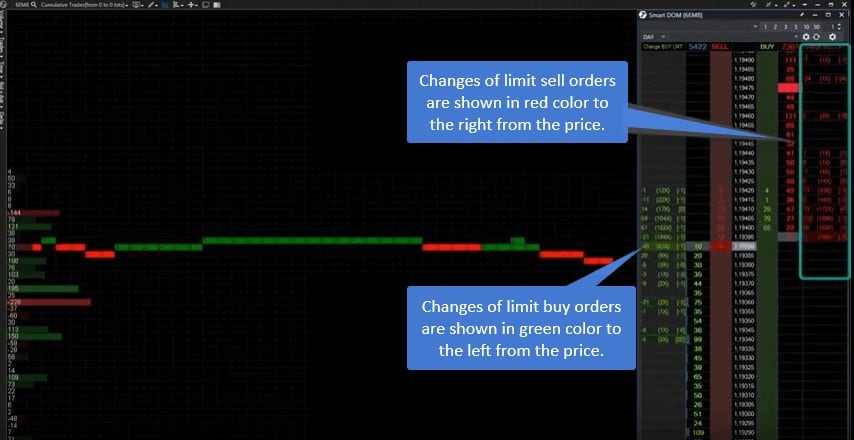
Changes of limit buy orders are shown in green color to the left from the price. Changes of limit sell orders are shown in red color to the right from the price. Bright green “flashes” highlight levels of changing the limit buy orders. Bright red “flashes” highlight levels of changing the limit sell orders.
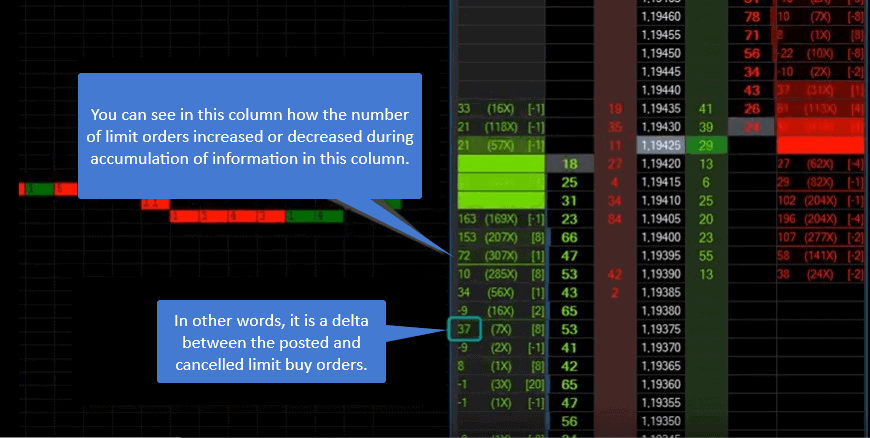
You can see in the left column how the number of limit orders increased, in other words, it is a delta between the posted and cancelled buy orders.
You can see levels, where changes were most frequent, in the middle column. A significant number of changes with respect to other price levels could testify to algorithm activity at this level.
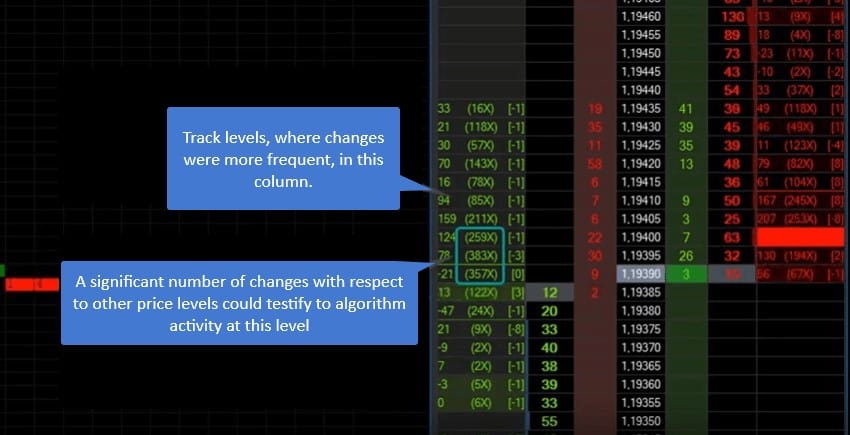
Posting or cancelling orders is reflected in the right column.